The first step to using your proxies is understanding how you want to ‘authenticate’ your IPs. The reason this is necessary is because we offer private proxy IPs, and we do not want anyone else to use them other than our clients. We offer both ‘IP authentication’ and ‘username / password’ authentication (SOCKS5 proxies are authenticated via username / password only).
On the authentication panel you will be presented with this page:
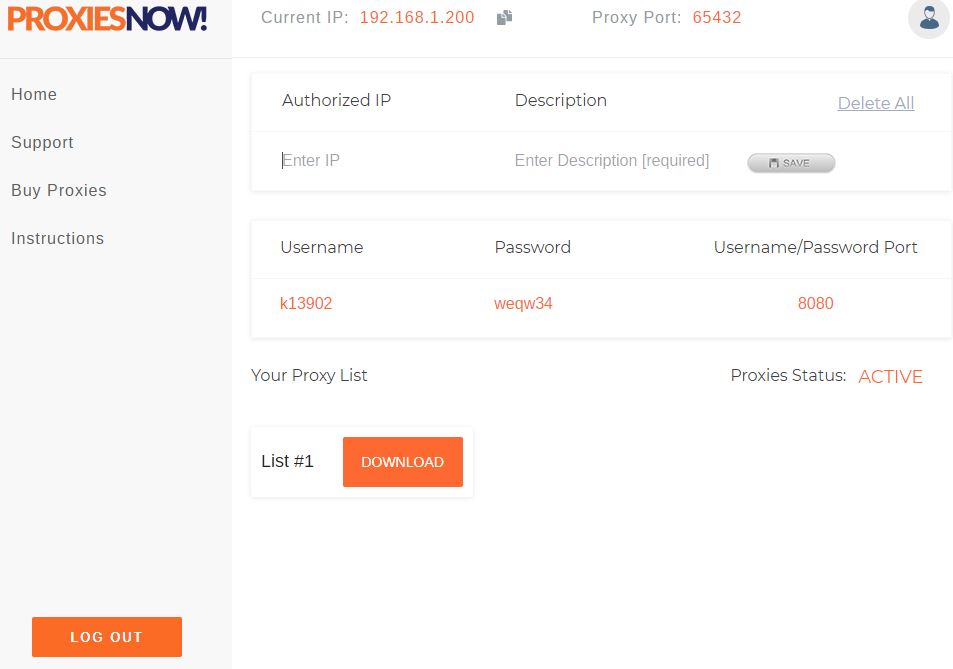
At the top of the page you will see the following:

- This is your current IP. The IP you are accessing the website from. This is displayed for your convenience if you would like to use the proxies from the computer your are currently accessing the website from.
- Clicking this file icon will copy your current IP to your clipboard. This will allow easier pasting to an authenticated IP field.
- This proxy port is the port you will use with the proxies if you are using IP authentication.
- Clicking this icon will take you back to the client billing area of the website.
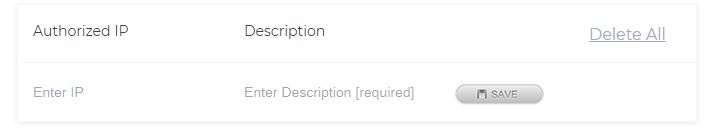
- The ‘Authorized IP’ field is where you will enter the IP of the computers you want to use the proxies from. If you want to use the proxies from your current IP you can paste this here from the “Current IP” field at the top of the screen. Once an IP is entered please allow 5-10 minutes for this to be recognized by our system.
- The ‘Description’ field is where you will enter a description of the IP you entered. You can enter anything here to describe the IP; such as ‘home computer’, ‘work server’, or whatever you would like to describe the location or purpose of this authentication.
- Once you have the IP and description entered click the ‘SAVE’ button. Your IP is now authenticated.
- The ‘Delete All’ button will remove all of your authenticated IPs.
If you update or change an IP be sure to click ‘SAVE’ as well!
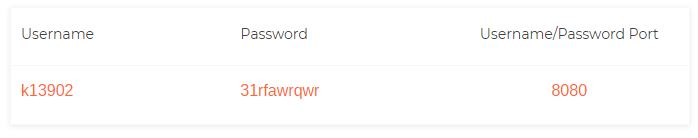
This area contains the username, password and port. Using these credentials with your proxies will bypass the IP authentication, you will not need to authenticate your IP.

At the bottom you will see the following. Clicking ‘DOWNLOAD’ will immediately download your proxy list.
If you have any questions or problems please click here to contact support.
